Qualys Community Edition in a small business environment
For many years I’ve used Qualys vulnerability management tools in secure, professionally hosted and segmented hosted environments. The scans and the reports generated were just what we needed to satisfy the PCI requirements, justifying the considerable yearly subscription price. When in June 2018 Qualys announced their Qualys Free Community Edition aimed at small organizations, and I was eager to try it out. Compared the paid editions, Qualys CE understandably has some limits. Not all applications from the Qualys suite are available. Only the scanning of 16 IP addresses (internal or public) is allowed, and only 1 Web application Scanner is available. Furthermore, only one local appliance can be deployed, so only one internal network can be scanned.
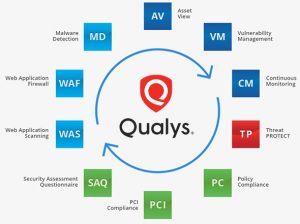
Qualys suite
Getting started
Getting started with Qualys CE is easy. Registration can be done here, To scan your internal network you will need to download the virtual appliance, and register it with the Qualys Platform. Use the Discovery scan to get a list of assets (hosts) present on you local network, and check the open ports. This might be where you get the first surprises. What is really active on your network?
Vulnerability Scan
This is where it gets interesting. Select up to 16 internal or external IP addresses to be scanned. This is the basis for either an on-demand scan, or future scheduled scans. There are many options to choose from, but often the defaults are fine. To scan the internal network, select the virtual appliance you downloaded earlier. I also recommend performing some external scans using the external (Qualys) scanner, targeting your external IP address, to see what is vulnerable from the outside. The internal scan took about 35 minutes on my network, but it probably depends on the number of open ports.
Web Application scanning
Qualys Community Edition package also includes Web Application scanning, although the CE is limited to one web application only. There are many settings to tweak the scan to your needs. Even complicated Selenium scripts can be included in the scans. It is unfortunate that contrary to the vulnerability scans, the Web Application Scans cannot be scheduled.
Cloud agents
A different way to scan the infrastructure is the use of cloud agents. These are small programs that are installed on the computers of the network. Agents can be downloaded for Linux, Windows, IBM AIX, and OSX. From the inside of the computer, they can detect things that cannot be detected easily from the outside. The agents can for instance detect software that needs updating.
Results
By default, both the vulnerability scan and web application scans may give a lot vulnerabilities. And this is where things get more complicated. What are false positives, what can be ignored, and what should be rectified immediately? Of course, all vulnerabilities are ranked by threat level, and Qualys does an excellent job at giving additional information about the vulnerabilities found. One the other hand, the discovery scan only sees devices which respond to ICMP (ping) messages, so rogue devices can still be hiding in your network without being detected. The cloud agents work really well, the day after Adobe reported a vulnerability I could see which of my system contained the problem. Scanning from the outside proved useful, and pointed out that some application used uPnP to unintentionally forward a port on my router. More on the vulnerabilities found on my personal blog.

OpenVAS
For comparison, I installed a virtual OpenVAS scanning instance and let it scan my network. Obviously there are no limits here, as the product is free. Using docker on CentOS 7, the installation isn’t the hassle it used to be. OpenVAS detected a default username and password on a switch, which was interesting.
Conclusion
It is easy to perform a vulnerability scan of your network with Qualys CE, and it is likely to reveal vulnerabilities that need to be addressed. To keep the systems secure, these duties must become part of the daily business. With the ease of installation and use of cloud solutions like Qualys CE, comes an issue of trust. Users of Qualys CE are giving a third party very sensitive information about their network, which is a security risk . Whether this risk is acceptable is a personal decision.
